The #MondayMusings Industrial Transformation blog series provides insight and analysis for executives from the previous week’s briefings, events, and publications @LNSResearch.
Click here to speak with Matthew Littlefield
Over the past several months I have had briefings from numerous executives touting their company’s new and updated solutions for Industrial Cyber-Security, including Bob Honor at Bedrock Automation, Susan Peterson-Sturm at Honeywell, and Ron Victor at IoTium. These companies are investing heavily to embed next-generation security capabilities into industrial networking, industrial automation, and IIoT offerings. Unfortunately, these solution providers are facing an uphill battle. Most industrial companies today are woefully behind when it comes to investing in ICS capabilities. What’s more, despite the significant adoption plans industrial companies have for the IIoT, there is a scary lack of planned adoption for ICS capabilities in the future.
In this blog post, we will examine how these market forces are creating the potential for the perfect storm in the ICS market and what industrial companies should do about it.
2017: The Year of Adoption for the IIoT
LNS Research has been helping define and tracking the IIoT market since 2014.
2015 was the year of introduction for the IIoT. Our research of over 1,000 surveyed industrial companies showed that 40% of companies at that time did not know or understand the IIoT. 2016 was the year of education, based on the hard work of analysts at LNS, along with many other voices in the marketplace, the number of companies that didn’t know or understand the IIoT dropped to 19%, while the share of companies planning to adopt the IIoT increased by ten percentage points.
Based on this trend, LNS Research expects that 2017 will be the year of adoption for the IIoT. We have already predicted that many of the leading industrial companies will be moving out of the planning/pilot stages this year and making enterprise commitments to deploying IIoT Platforms.
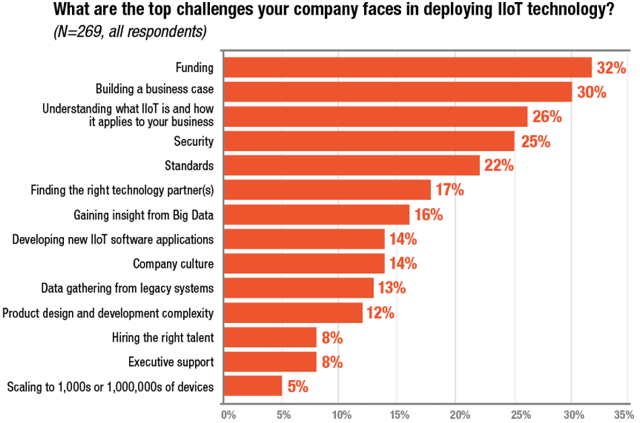
Unfortunately, we have not yet seen these adoption plans bleed over to the ICS market. In fact, security challenges are only #4 in our recent survey.
Woefully Low Current and Planned Adoption for ICS Capabilities
In our most recent survey on the IIoT, ICS was one of our main areas of examination. When we asked industrial companies what ICS technologies and best practices were currently adopted, other than Firewalls and Access Control, the adoption rate was below 25%. Even scarier, when asked what was the planned adoption by the end of 2017, there was no significant movement in these numbers.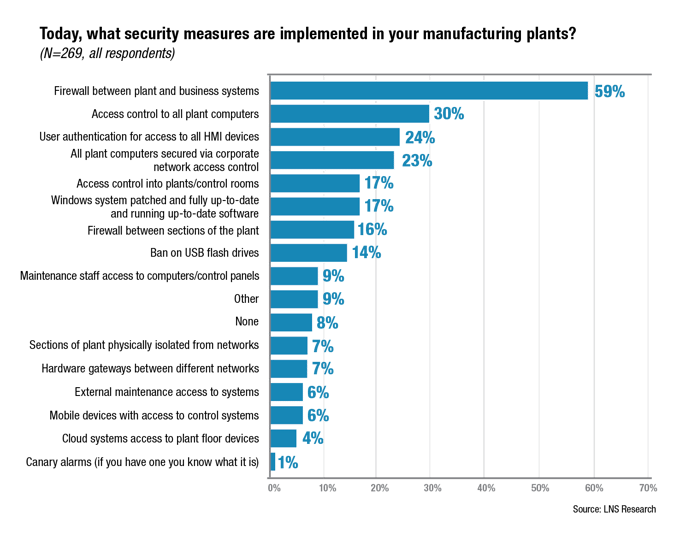 This means 75%+ of plant floors today are currently behind when it comes to adopting ICS best practices and are ill equipped to start deploying IIoT technologies or defend against a coordinated cyber-attack.
This means 75%+ of plant floors today are currently behind when it comes to adopting ICS best practices and are ill equipped to start deploying IIoT technologies or defend against a coordinated cyber-attack.
The Brewing Perfect Storm
With industrial cyber-security events like Stuxnet, Saudi Aramco, ThyssenKrupp, Unnamed German Steel Mill, and many more occurring since 2010, there will eventually be an industrial cyber-security event that changes the consciousness of society; creating a “new normal” where the above survey results become completely unacceptable.
It may be tomorrow, it may be in a year, or it may be longer; but one day we will all realize that without a robust, risk-based, approach to ICS that is bottoms-up and not bolted-on, we will not be able to ensure safety in our industrial facilities and we will lose our social license to operate.
As industrial companies move to aggressively deploy the IIoT over the coming years; if they do not take a platform approach that incorporates ICS capabilities into the very fabric of these solutions, the entire industry is at risk. If new IIoT capabilities are instead just added on to legacy automation solutions without consideration of architecture and ICS, when the brewing storm hits, most companies will not be able to respond in time to withstand without significant damage.
To learn how to be prepared for the storm and take a platform approach to the IIoT that incorporates the needed ICS capabilities.
