The #MondayMusings Industrial Transformation blog series provides insight and analysis for executives from the previous week’s briefings, events, and publications @LNSResearch.
Click here to speak with Matt Littlefield
LNS Research is deep in the throes of completing the draft of our 2018 Industrial Internet of Things (IIoT) platform solution selection guide. As part of that guide development, we revisit and update our 2014 IIoT platform model.
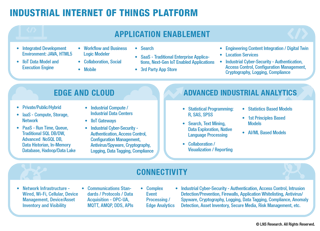
Some notable changes to the model from its launch in 2014, include:
- Application development now expanded and described as application enablement
- Cloud now expanded to included Edge and Cloud
- Big Data analytics now redefined and expanded as advanced industrial analytics
- An increased focus on and unified definition of industrial cyber security
Industrial Cyber Security
In this post, we will focus on our expanded coverage of the industrial cyber security space. Since the advent of the IIoT platform space in 2014, one of the biggest areas of change has been in industrial cyber security. Industrial cyber security is nothing new, and for decades now there has been a robust ecosystem including:
Industrial cyber security services offerings from large automation and consulting organizations that typically include
- Benchmarking
- Audits
- Risk assessments
- Remote monitoring
Traditional cyber security technology, targeting the operational technology (OT) environment that typically includes:
- Authentication
- Access control
- Intrusion/threat detection
- Firewalls
- Application whitelisting
- Anti-virus/spyware
- Cryptography
- Logging
- Data tagging
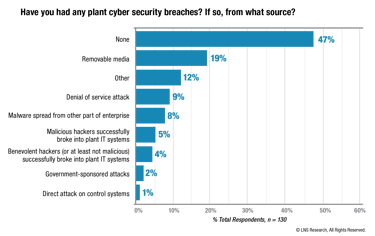 However, these capabilities should now be considered necessary but insufficient to meet the imminent industry threats. Even though LNS Research survey data shows that large majority of cyber attacks on plant networks are targeting IT not OT systems.
However, these capabilities should now be considered necessary but insufficient to meet the imminent industry threats. Even though LNS Research survey data shows that large majority of cyber attacks on plant networks are targeting IT not OT systems.
There is evidence this is changing and accelerating. Just last month there was a new high profile attack on an OT system, and for the first time, it was an attack on the safety system itself.
Advanced Industrial Cyber Security Vendors Emerge
Thankfully, there is a new generation of industrial cyber security specialist vendors emerging, what LNS refers to as advanced industrial cyber security vendors, with offerings that typically include:
- Industrial network visibility and passive monitoring
- Asset inventory
- Anomaly detection
- Risk management
- Secure media
LNS is currently tracking 7 Advanced industrial cyber security vendors that fall in this category: Claroty, CyberX, Dragos, Indegy, NextDefense, Nozomi Networks, SecurityMatters; and this post covers three of those vendors that recently briefed LNS Research.
Claroty
Claroty is an Israeli company that launched publicly in 2016, and has since moved its headquarters to New York City. In just a few short years the company has emerged as one of the early leaders in the advanced industrial cyber security space, with:
- An impressive set of investment rounds raising USD 32M
- Several secured automation partners like Rockwell Automation and Schneider Electric
- Relatively large R&D team compared to peers
The company’s platform is completely passive and provides visibility into the lowest levels of industrial cyber security networks. The platform's capabilities include continuous vulnerability detection, continuous threat monitoring, secure remote access, asset visibility, and security alerts in an operational context.
Indegy
Indegy, founded in 2014, is another Israeli company headquartered in New York City. The company has received USD 20M in funding to date and has an impressive list of 60 customers that goes across critical infrastructure plus other industries that are less focused on cyber security, like food and beverage and automotive manufacturing.
The company offers asset discovery, asset visibility, asset inventory, dashboarding, alerts in an operational context, and network monitoring for anomalies. Two unique aspects of the Indegy solution include a hardware component (Indegy Management Servers and Indegy Sensors) and the company’s Agentless Controller Validation, which means its solution is not entirely passive; it can map the network without having to wait for traffic.
Nozomi Networks
Nozomi Networks founded in Switzerland in 2013, and moved its headquarters to San Francisco in 2016. The company has secured USD 24M in funding to date including a recent USD 15M second round funding. The company’s product is called SCADAGuardian and includes network visualization and modeling, asset inventory, threat/anomaly detection, vulnerability assessment, dashboards, and reporting.
The company has demonstrated early capability to sell and deploy successfully to customers headquartered in global regions including North America, Europe and the Middle East. It has also won an impressive partnership with FireEye, the company that first identified the TRITON attack.
Time for Action
Claroty, Indegy, and Nozomi Networks represent three companies from an emerging set of vendors that will play a critical role in both securing critical infrastructure and enabling the growth promised by the IIoT and Industry 4.0
LNS Research recommends that industrial companies no longer view industrial cyber security through an ROI lens or as a nice to have. It goes right to the core values of a company, like safety, quality, and operational excellence. If a company can’t efficiently guarantee cyber security in operations, it can’t effectively ensure safety, quality, and operational excellence either.
To learn more about the LNS perspective on industrial cyber security and the broader vendor landscape read the eBook, Putting ICS at the top of the CEO Agenda.