ICS Cybersecurity...Twists, Turns, and Roadblocks
LNS Research Analyst Joe Perino examines the state of cybersecurity offerings and the importance of cybersecurity as a key element to risk management.
Last April, we wrote about the market twists and turns in the dynamic cybersecurity software market and the challenges and barriers to progress. More recently, we published an M&A update that noted the acquisition of PAS Global by Hexagon AB. Recent conversations with end-users, cyber-software, and automation vendors have highlighted the importance of not just the software but of the associated set of services so vital to implementing and maintaining cyber protection. This raised the question of the best way for most end-users to approach this, get the right help, and bridge the cyber gap between IT and OT. The answer is less a technical discussion than it is about strategy, standards, policies and procedures, and partnering services.
There are a number of issues facing end-users in deciding how to deal with cybersecurity:
For example, see the excellent article by Exida’s Patrick O’Brien in the August 2021 issue of Chemical Engineering Progress.
We are sure the reader could add to this list.
So, what do we do about it? What’s the right way to bring IT and OT together to support Operations? And, who should be your partners?

First, the good news is that LNS Research increasingly sees IT and OT cooperation on a number of fronts and, in particular, Industrial Transformation (IX) programs. IX Leaders tend to have converged organizations, including IT and OT, to help co-architect the foundations for scalable solutions, with cybersecurity being an integral part of the scope. In addition, OT is learning more and more IT and vice-versa, and cybersecurity is now becoming part of the routine HAZOP process.
Nevertheless, this still leaves open the question of how to support plants and supply chain operations across a wide geographic footprint and range of simple to complex operations and associated systems.
There are five main choices:
Let us clarify that the large IT services firms do system integration, but we are talking about SI services at the OT level, ISA 95 levels 1 to 3. Also, I am not counting cybersecurity software vendors here because they primarily want to sell software and no more services than necessary to guarantee uptake.
Corporate IT resources are always limited and, thus, likely focused on supporting the back-office applications, the corporate network, business continuity operations, and managing major IT vendors relationships, including outsourced services and cybersecurity software selection. OT resources are even thinner as IT services have been used to handle problem resolution, plus retirements of senior personnel intimately familiar with the locations, equipment, and technologies. The Colonial Pipeline case is a good example. CEO Joseph Blount is quoted as saying, “workers who know how to manually operate the Colonial Pipeline and other infrastructure have mostly retired or died.”
IT services firms are natural partners to help corporate IT with the aforementioned tasks but struggle to support real-time OT systems. They typically lack the depth of skills to do so, the local presence, if needed, and find it difficult to make a business of OT support. Some have made moves to acquire OT services, but in general, independent SIs are reluctant to be acquired by IT services firms. For example, more than one LNS Research client has told us that they cannot find services firms that can span IT, OT, and understand manufacturing and supply chain operations.
The vast majority of system integrators in North America and Europe are small companies with less than 100 employees. Generally, they pursue project work and not 24/7 support services. There are exceptions, of course. A few have large footprints, including international offices, which could fit the bill. They have added cybersecurity to their portfolio of skills and, thus, are a viable option.
Another alternative is to use an independent cybersecurity firm that specializes in managing OT systems. These firms might fit the bill for companies with smaller footprints and have the advantage of true neutrality. They typically have roots in the system integrator space so they, too, understand the OT world. Their limitation may be that they may not have the OT wherewithal and reach to serve large companies with significant geographic footprints. True, much of the work can be done remotely, but on-site capabilities are always an advantage. Nevertheless, this option is worth consideration.
The best alternative, particularly for global companies, are those firms already in the 24/7 OT support business - the automation companies. The major suppliers: ABB, Emerson, Honeywell, Rockwell, Schneider, Siemens, and Yokogawa have all made significant investments in being able to support the new OT Ecosystem, as a result of client demand as well as the move to Edge and Cloud with their products and services, including cybersecurity. These firms have either acquired cyber software companies or partnered with a leading ICS cyber supplier, such as Claroty, Nozomi, Dragos, ThreatConnect, and many others. For example, LNS Research has long relationships with all seven companies and has done specific cybersecurity work for Honeywell and Schneider Electric. Together, they bring their ecosystem of partners for various functions, for example, CISCO, for networking. In addition, to working with a client’s specific suppliers, say Splunk.
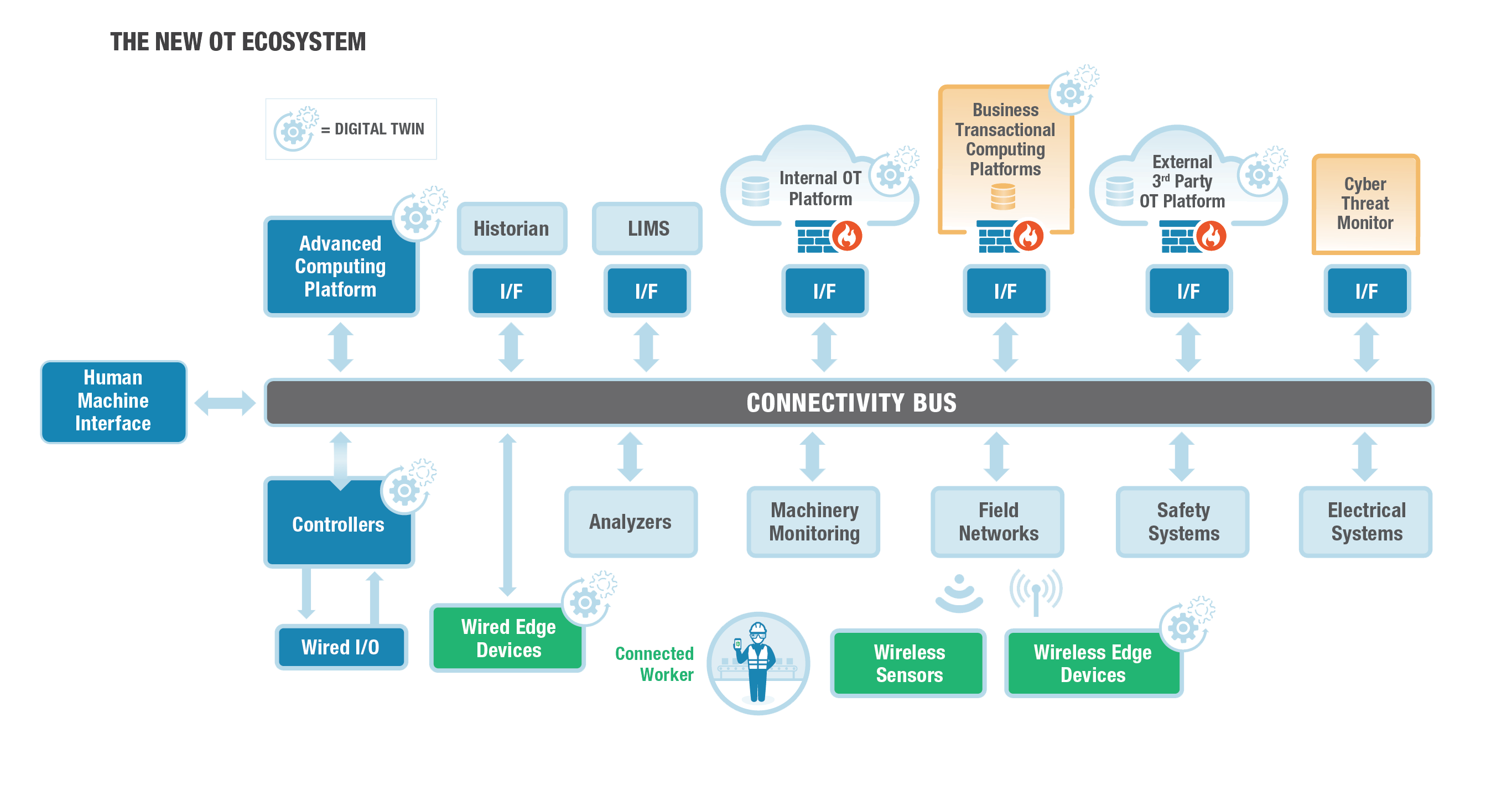 Figure 1 - The New OT Ecosystem
Figure 1 - The New OT EcosystemThe other advantage is that some can support a Level 2 multi-vendor environment because they acquired SIs who still work with competitors’ systems. Such is the case for Rockwell Automation® who acquired Maverick, and Emerson, who acquired The Automation Group (TAG). With their increased IT capabilities paired with deep OT and industry domain knowledge, they are well prepared to take the 3 a.m. call. Perhaps the only area they may lack fluency in at present is being able to support the wide variety of the wrap & extend IIoT solutions now being proffered in the market. But then again, who can?
For owners and operators, it pays to look at cybersecurity through the same managed service lens that you already use for sourcing help at both the IT and OT levels, be it networking, Cloud, and desktop support at the corporate level or automation, maintenance, and engineering at the plant level. Avoid trying to grow the corporate IT organization into OT, instead, take a managed team approach by partnering with those organizations that can best serve manufacturing’s needs. The right partners can relieve a lot of 3 a.m. headaches.
Second, automation vendors and SIs are learning the IT environment. Why? Because they have to deliver the new OT Ecosystem. IT is not expected to learn how to cyber-protect PLCs, but OT knows PLCs inside and out and, thus, has trained IT personnel in OT environments for exactly that reason. When you absolutely have to, you do.

Third, recognize who your internal client is and align your metrics accordingly. Keep score the right way. Most IT metrics like process compliance, percentage of revenues, and SLAs are internally focused on IT, not OT or Operations. A mere 1% increase in production or a 1% decrease in downtime is likely worth far more than a 20% savings in IT spend. Spending on cybersecurity is no exception and is probably underfunded across both IT and OT.
For cybersecurity services providers, you must have value propositions for both IT and OT. You can make a powerful argument to partner with IT and OT to deliver a more secure business. But don’t rely on OT to sell you to IT. You must engage IT on their territory and check off all of their criteria. Yes, again, you will run into DIY as nearly all vendors do, so show how you compliment IT, not compete with them.
One additional challenge that the automation service providers will face is that they have built partnerships with the leading OT cyber vendors but they also rely heavily on their big IT partnerships – Microsoft, Cisco, HPE, etc. – and both Microsoft and CISCO have bought competitive OT cyber software vendors, that may not have had commercial success but did have the technology. So, this is a channel conflict that will have to be managed.
In summary, addressing cybersecurity is a critical part of risk management, and hence, achieving sustainability. It cannot be left as a contention point between IT and OT that is not properly and fully addressed. Choosing the right partners can go a long way to ensuring the safety and continuity of the business.
All entries in this Industrial Transformation blog represent the opinions of the authors based on their industry experience and their view of the information collected using the methods described in our Research Integrity. All product and company names are trademarks™ or registered® trademarks of their respective holders. Use of them does not imply any affiliation with or endorsement by them.
As a member-level partner of LNS Research, you will receive our expert and proven Advisory Services. These exclusive benefits give your team:
Let us help you with key decisions based on our solid research methodology and vast industrial experience.
BOOK A STRATEGY CALLLNS Research Analyst Joe Perino examines the state of cybersecurity offerings and the importance of cybersecurity as a key element to risk management.
Industrial companies no longer view Industrial Cyber Security through as a nice to have. It goes right to the core values of a company, like safety,...
In this monthly Roundup, LNS Research explores recent announcements and events, such as automotive supplier digitalizing; new IIoT tech framework;...
The Industrial Transformation and Operational Excellence Blog is an informal environment for our analysts to share thoughts and insights on a range of technology and business topics.